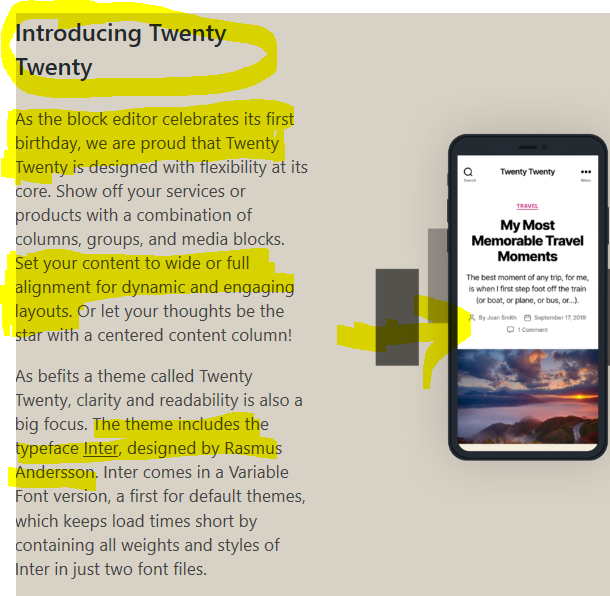
If you ever had the relatively common issue with Windows 10 desktop right-click failing, I may have an answer. I had the displeasure of this occurring recently on my Lenovo IdeaPad Flex 5. This is a fine 2-in-1 computer. It is really nice, both in tablet mode [after folding over] or in traditional laptop mode. But after a year of Android and Visual Studio and other bulky application installs, it started to get cluttered with software, an issue of my own making. So, time for a refresh! I verified everything I needed was already synced or backed up to One Drive.
I reset my Windows 10, mainly to refresh my system so that it was like brand new. I went through the “Reset this PC” process successfully. Mission accomplished. One glitch after completion: while trying to get to the simple desktop personalization settings to extend my 2nd monitor, I noticed that right-clicking was not working. It even locked up my laptop completely a few times. In addition, sometimes it WOULD open after about 20 seconds, although sometimes not at all. It was driving me crazy. I restarted multiple times. Should I clean things up a bit on the OS? There was nothing to clean up, as this was literally a fresh install.
I did the usual Internet searches. I tried Google and Microsoft’s support pages, but kept getting odd answers, such as “reset your system” [hey, I JUST did that!] or “just go into the registry and make a simple change”! I am not scared of the Registry, but there is NO WAY this should be needed in order to fix what SEEMED to be a Microsoft related issue. Microsoft has had its fair share of issues over the years [for sure!] but right-clicking on the desktop is not one of them. So I checked the Event Viewer and noticed it was mostly clean, with the usual assortment of harmless warnings and generally useless “Information / Service Control Manager” events … except for ONE that stood out:
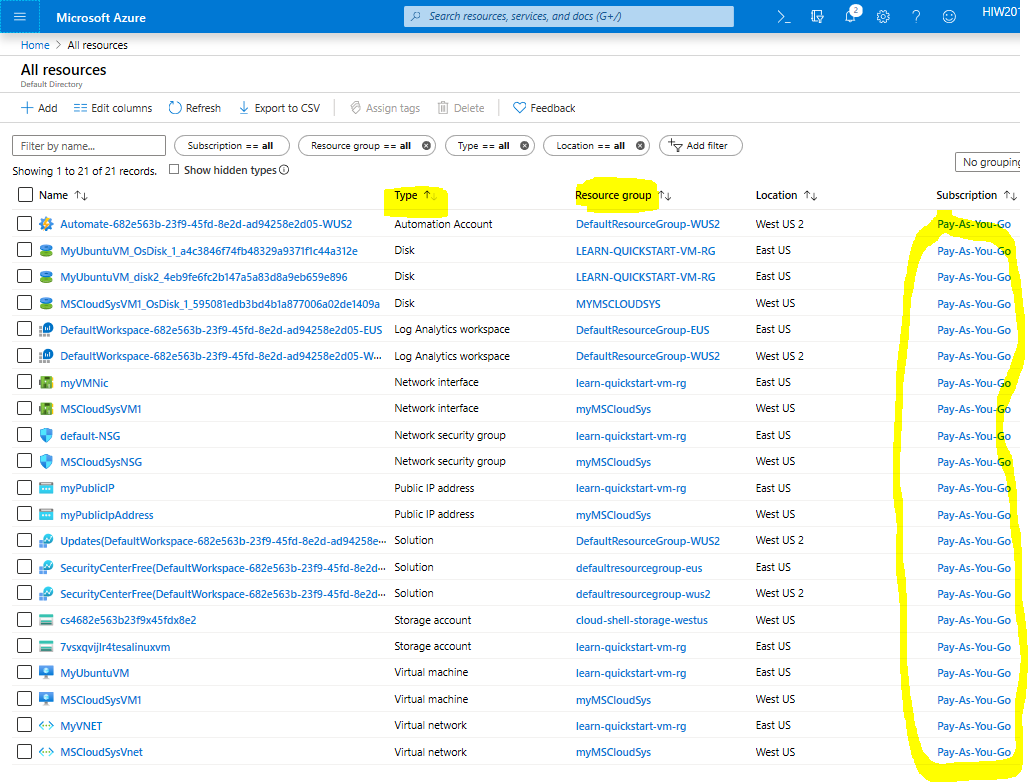
Event Logs

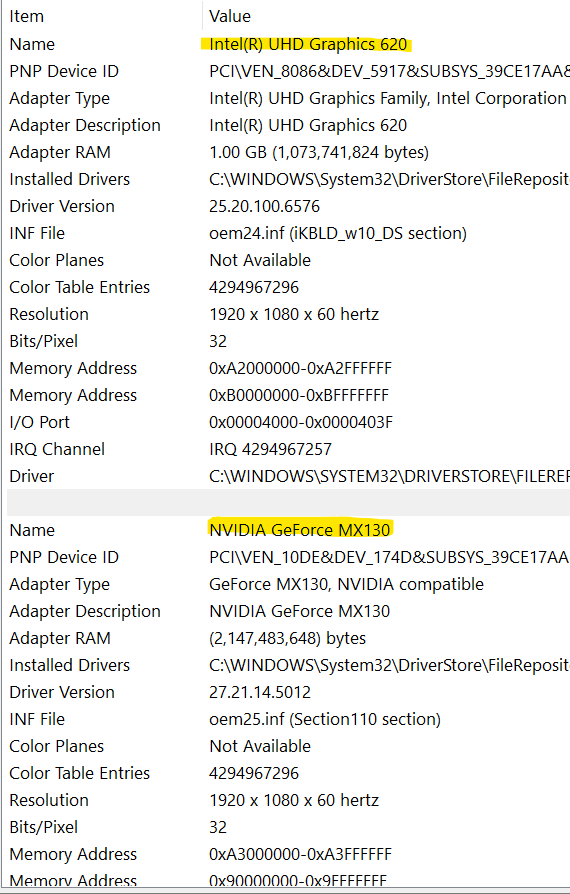
Now this one was interesting. The log error is a red error, and it is non stop, essentially flooding my event viewer since I reset the Lenovo’s Windows 10. I assumed if I simply updated Nvidia software, all would be good, but alas, their update tool told me I was up to date. The only thing to try was completely removing the NVidia software – all of it, then maybe reinstall. There is a control panel and a display driver. You will NOT lose graphics or your monitor view if you do this. If anything, Windows will default to generic drivers. But the reality is that my laptop, like so many modern laptops has TWO graphics interfaces [usually Intel and NVidia], per below image. Why two? Intel handles most graphics tasks. NVidia is used mainly for highly intensive tasks, such as gaming or video editing, maybe 3D. I do not work with those tasks, so I removed every NVidia application from the Windows 10 “Add or remove programs”. Success! I can now right-click on my Windows 10 desktop, and it feels so good! I will not be reinstalling NVidia software any time soon until they can fix this.
I also feel better not having a flood of NVidia related error messages in Event Viewer. All the red errors are now gone. Sometimes people lash out at Microsoft for things like this, despite the root cause of the issue emanating from a graphics or other hardware vendor.
2 Graphics Cards