Microsoft and others have helped to expedite moving the Ukrainian government’s systems to the cloud. They are offering various forms of monetary assistance, presumably with hosting, integration, migration, and especially, cybersecurity, according to this article. Russia continues to be a formidable worldwide cyber power and threat.
Microsoft Edge Flaw
It looks like Microsoft Edge has caught the same bug or flaw that recently affected Google Chrome! If your Edge browser gives you an update notification (look for the symbol in the upper right of Edge), install / restart the Edge browser right away.
Microsoft Edge has urgent security flaw — what to do now (msn.com)
Me too!

https://www.darkreading.com/threat-intelligence/cartoon-phishing-intelligence-/d/d-id/1337593
FREE Trend Micro House Call
Did you ever get that feeling that your computer was acting “funny” or was “too slow”, in an unusual sort of way? Or maybe you read a recent article about the latest malware or creepy hack attack that got you thinking about hijacked video cameras? Sometimes hacks can bypass your traditional antivirus or endpoint security. Every once in a while, I like to run the Trend Micro awesome free security scan.
There is nothing wrong with double checking your current security software! Two eyes are better than one. Trend Micro has a long track record in the security software world. They are well regarded and this is a very solid offering. Obviously, the fact that it is free makes it even better! It can be downloaded and quickly installed and run right away. Always run a full scan in this case [not the quick scan]- go big or go home, so to speak. If Trend Micro is currently in use, try the McAfee free option.
So far, so good:
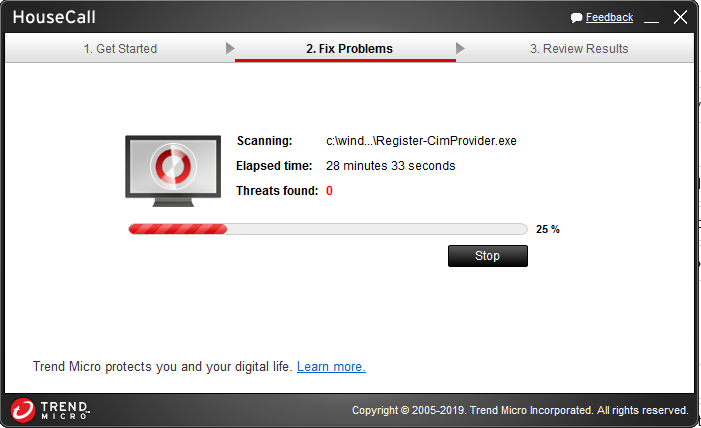
Grab the free security scan here
Antivirus Companies Hacked?
In a nutshell: the cybersecurity companies that design software that is intended to protect our computers … got hacked. Therefore, it is fully possible that now the hackers understand the defense mechanisms of the companies that fight cybersecurity, at least at the PC, Mac, workstation level and maybe more. This is not good!
Details are sketchy, as is common with these hacks, and two of the victims [Norton and McAfee] deny any breach, but Trend Micro admits a breach occurred. Although Trend said the hack only affected their “lab”, this does not necessarily make customers feel any better about it, given they are in the CYBERSECURITY industry.
Live Cyber Attack Threat Map
This “Check Point” [or “ThreatCloud”] cyber attack map is mesmerizing. It is a live cyber or hack attack map containing oodles of attack lines that follow live, currently in progress cyber attacks. The threat map lists the time, the attack name [or virus or hack type], the source and the intended victim location: the target.
The attacks are unrelenting and endless and the lines are ongoing in this dynamic situation.
One take away I have is that every country in the world can be a cyber target. Likewise, attack sources seem to come from almost anywhere in the world, although ‘botnets’ [a group of secretly hacked, controlled computers] are likely a major factor in this.
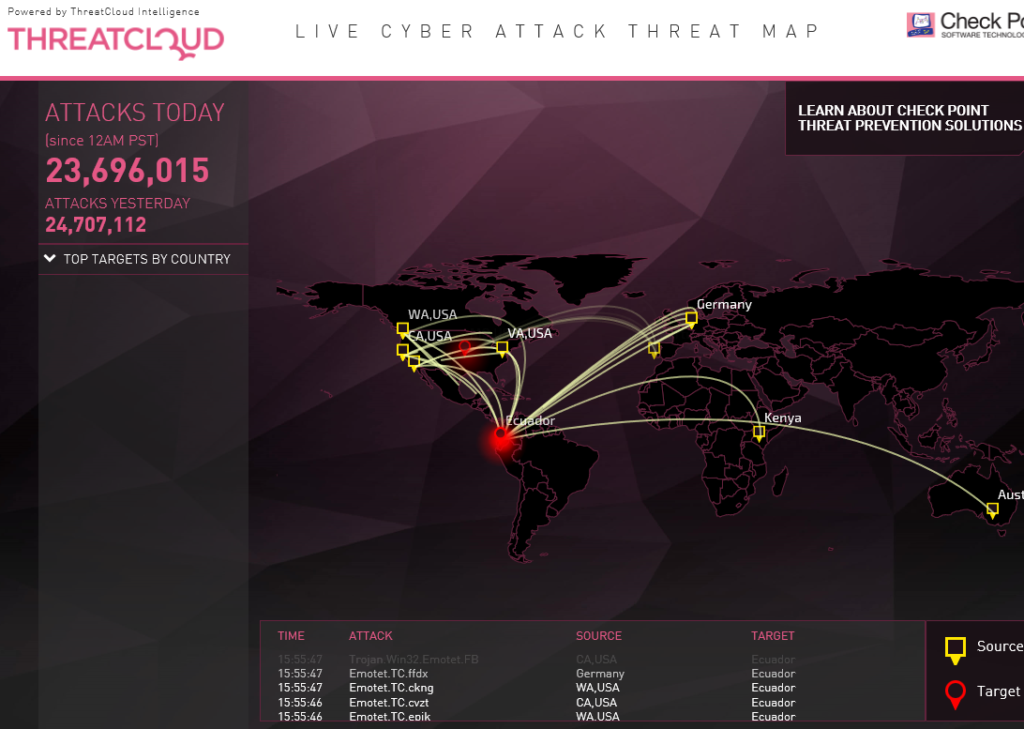
Here is the web address for the live map:
Atlanta hit by ransomware attack
This is actually [indirectly] courtesy of the US Government’s NSA, from a few years ago. They actually created the code that exploits Microsoft Servers that face the internet directly.
“It’s been almost a week since the City of Atlanta was hit by a ransomware attack, which encrypted city data and led to the shutdown of some services.
Mayor Keisha Lance Bottoms said in a press conference Monday that the city’s government is working on recovering the network after ransom notes appeared on computer displays on Thursday afternoon. The city has hired local cybersecurity firm SecureWorks to assess the situation.
Reports say the notorious SamSam ransomware was used in the Atlanta attack, which exploits a deserialization vulnerability in Java-based servers. Details of the attack remain largely unknown, but an early investigation may have identified who is behind the attack, said SecureWorks chief executive Michael Cote. Almost a million dollars has been reaped from other businesses that were infected and paid the ransom. It’s not known if Atlanta will pay the ransom.”
Backdoor in Captcha Discovered
Nothing to see here, folks …
“Backdoor in Captcha Plugin Affects 300K WordPress Sites”
“The WordPress repository recently removed the plugin Captcha over what initially appeared to be a trademark issue with the current author using “WordPress” [Editors note: the original page has been removed, we’re now linking to a screen shot.] in their brand name.
Whenever the WordPress repository removes a plugin with a large user base, we check to see if it was possibly due to something security-related. Wordfence alerts users when any plugin they are running is removed from WordPress repo as well. At the time of its removal, Captcha had over 300,000 active installs, so its removal significantly impacts many users.”
Incredible analysis in the below link. Nicely done by WordFence.
Blocked Countries by WordFence
“China is in the lead” … of blocked countries. My humble website is constantly being sniffed at from the outside. To me it makes no sense on the surface – I have no confidential data or business secrets whatsoever. I do not do eCommerce or any business transactions for that matter. I do not even make poor stock market predictions!
But it makes sense to the potential intruders. These are likely bots just doing recon, searching for WordPress, Plugin or theme weaknesses and other possible pots of gold. Thankfully, I am fully invested in “WordFence”, an outstanding WordPress firewall.
Equifax Breach or Hack
This is the only link [the first one, below] or site that matters when it comes to the Equifax hack. There are many phishing websites disguising themselves, and reports are coming in that hoax or fake emails are popping into Inboxes. Use caution. ONLY go through Equifax, seeming as though they are the ones who caused the mess. As they likely already have your identity, and then lost it via a hack, you may as well follow the steps off the link below to get yourself courtesy identity theft protection for a few years [that is their penance].
I would even emphasize that you should not take my [or anyone’s] word for it, and double check on Equifax’s website yourself.
https://www.equifaxsecurity2017.com
Cross reference with the FTC:
https://www.consumer.ftc.gov/blog/2017/09/equifax-data-breach-what-do


