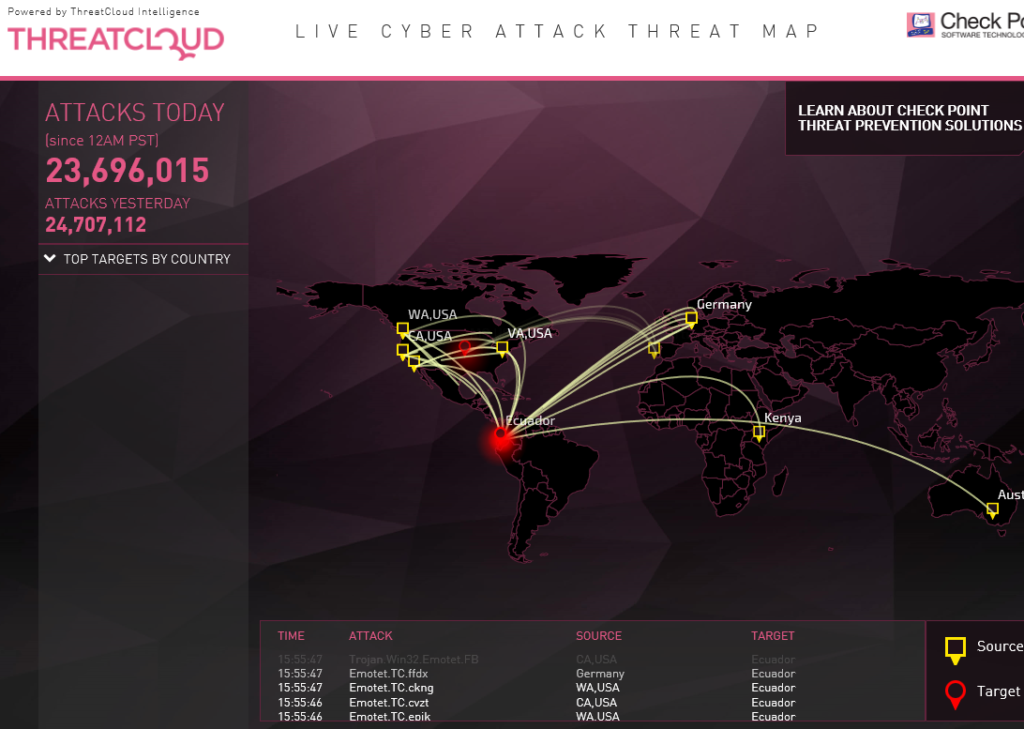
I use Veeam back up software for Microsoft 365 backups. It is an excellent, efficient, and effective backup program. It is used specifically for team SharePoint sites, user mailboxes, and user OneDrives (‘My-SharePoint’). I installed the needed Veeam modules on a standalone Azure virtual machine which communicates to our related cloud services. Although this article is very useful, the headline is a bit misleading. 76% of organizations have not admitted to paying ransomware to criminals so they could recoup locked data. But 76% of organizations affected by ransomware did pay ransomware to hackers. Per Veeam’s survey: (we) “surveyed 1,000 IT leaders whose organizations had been successfully attacked by ransomware at least once during the past 12 months”. So, of those hacked, 76% had made some payouts. This is all very good information.
A very important additional piece of information is that 19% of those affected by ransomware (in this survey) did not need to pay any ransomware because … they had proper and secured backups. This, of course, is the objective. Ransomware breaches are failures in the penetration sense. But at least a proper organizational backup strategy can remedy any data loss. Once backup data is retrieved and restored, security breaches can be investigated, analyzed, and fixed.